Modernizing legacy systems is one of the most complex challenges in enterprise IT. Many organizations rely on monolithic applications built years—or even decades—ago. These systems are stable but difficult to scale, modify, or integrate with modern cloud-native technologies.
The common temptation? A complete rewrite.
Unfortunately, big-bang rewrites are risky. They often lead to missed deadlines, budget overruns, and operational instability.
This is where the Strangler Fig Pattern becomes a strategic solution.
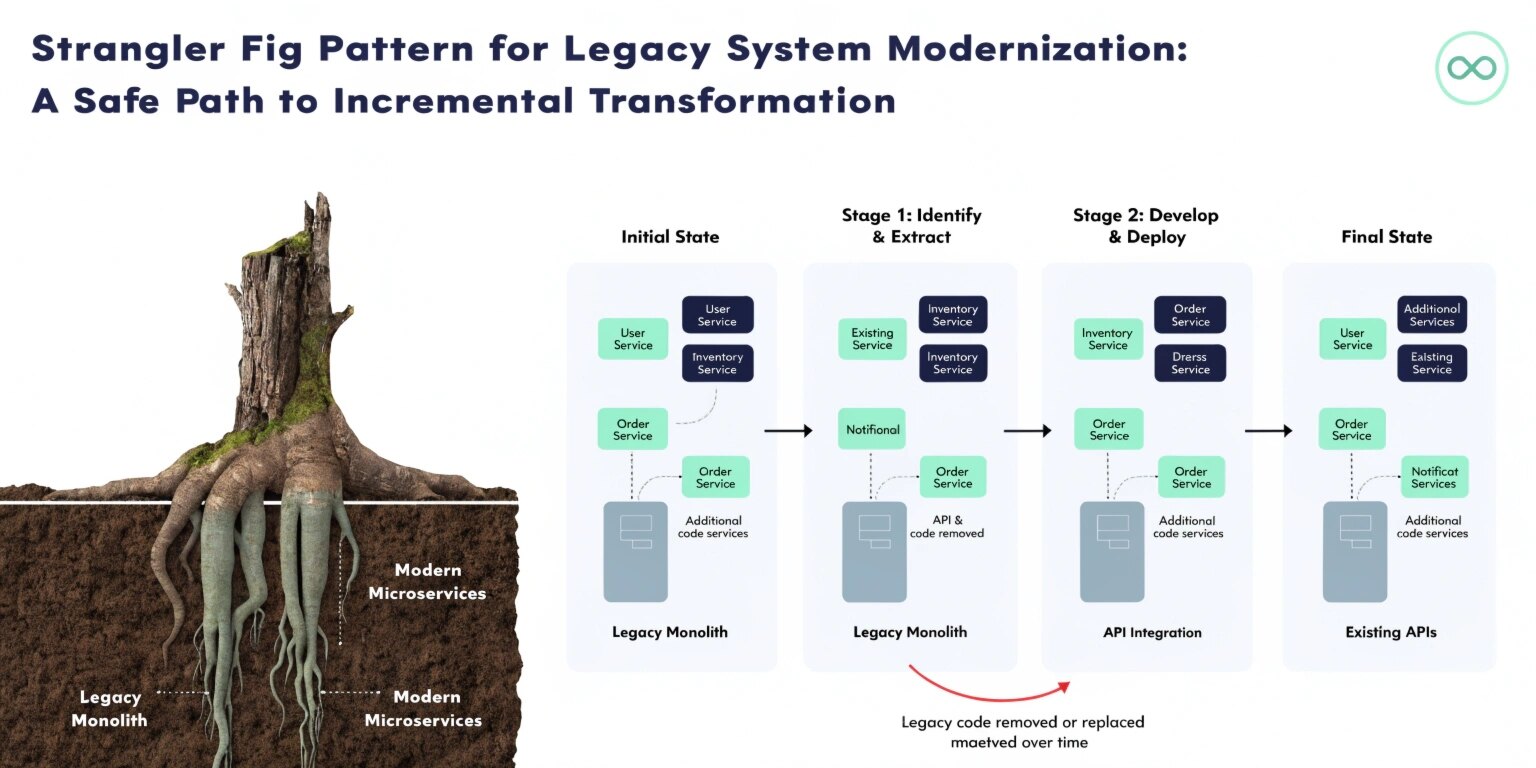
First described by Martin Fowler, the Strangler Fig Pattern takes inspiration from the strangler fig tree, which gradually grows around a host tree until the original structure is replaced.
In software architecture, this means incrementally replacing parts of a legacy system with modern services—without shutting down the old system.
The Core Idea
Instead of rewriting the entire monolith at once:
- Identify a small, manageable feature or module.
- Build a new service that replicates or improves that functionality.
- Redirect relevant traffic from the legacy system to the new service.
- Gradually expand this process until the legacy system is fully replaced.
This controlled evolution reduces business risk and allows continuous delivery.
Why Big-Bang Rewrites Fail
Complete rewrites introduce major challenges:
- Loss of undocumented business logic
- Extended downtime risk
- Large upfront investment
- Resistance from stakeholders
- Hidden technical dependencies
Legacy systems often contain years of implicit knowledge embedded in code. Rewriting everything from scratch risks losing that value.
Incremental modernization preserves operational continuity while enabling gradual improvement.
Architecture Behind the Pattern
The Strangler Fig Pattern typically involves introducing a routing layer in front of the legacy system. This can be implemented using:
- API gateways
- Reverse proxies
- Load balancers
- Service mesh technologies
Incoming requests are dynamically routed:
- Old functionality → Legacy system
- Modernized functionality → New microservice
Over time, more routes shift toward the modern architecture.
Phases of Implementation
1. Assessment and Domain Identification
Start by analyzing the monolith. Identify bounded contexts or modules that can be extracted independently.
Using domain-driven design principles helps isolate business capabilities.
Choose components that:
- Have clear boundaries
- Have high change frequency
- Offer immediate business value
2. Introduce a Facade or Proxy Layer
Before extraction begins, introduce a routing mechanism. This becomes the control point for traffic distribution.
This layer ensures:
- No disruption to end users
- Seamless redirection
- Controlled rollout
The legacy system continues operating normally during this phase.
3. Extract a Single Feature
Select a specific feature—such as user authentication or order processing—and rebuild it as an independent service.
Key considerations:
- Database access separation
- API contracts
- Backward compatibility
- Data synchronization
After testing, route live traffic to the new component.
4. Monitor and Validate
Observability is critical.
Track:
- Performance
- Error rates
- Latency
- User impact
Incremental modernization only works when you can measure system health accurately.
5. Expand and Replace
Repeat the process across other domains.
Over time:
- The legacy system shrinks
- The modern architecture grows
- Technical debt reduces
- Scalability improves
Eventually, the monolith becomes obsolete.
Key Benefits
1. Reduced Risk
Changes are small and reversible. Failures impact only isolated components.
2. Continuous Business Operations
No downtime is required for full system replacement.
3. Incremental ROI
Modernization delivers value early instead of waiting years for a rewrite to finish.
4. Improved Scalability
Extracted services can scale independently based on demand.
Challenges and Trade-Offs
While powerful, the Strangler Fig Pattern introduces complexity.
Data Management Complexity
During migration, both old and new systems may share or duplicate data.
Strategies include:
- Event-driven synchronization
- API-based communication
- Gradual database decomposition
Increased Operational Overhead
Running parallel systems requires:
- Strong monitoring
- DevOps maturity
- CI/CD automation
Temporary Architectural Duplication
For a period, both systems coexist—adding complexity before simplification.
Real-World Example Scenario
Imagine a banking platform with a 15-year-old monolithic core system.
Instead of rewriting the entire application:
- Customer profile management is extracted first.
- Then transaction reporting.
- Then notification services.
Each new microservice integrates through APIs while the legacy core continues operating.
Gradually, the monolith becomes a thin shell until it can be retired entirely.
Best Practices for Success
- Start small—avoid large initial extraction.
- Maintain strict API contracts.
- Avoid shared databases between legacy and new services.
- Invest in observability and monitoring.
- Align technical modernization with business priorities.
- Communicate clearly with stakeholders about incremental goals.
Modernization is a journey, not a sprint.
When Not to Use the Strangler Fig Pattern
This pattern may not be suitable when:
- The system is small and simple
- The legacy application is nearing end-of-life anyway
- Business logic is too tightly coupled to isolate safely
- Operational maturity is low
In some cases, rebuilding may still be the correct strategy.
Final Thoughts
The Strangler Fig Pattern transforms modernization from a high-risk gamble into a controlled evolution.
Instead of betting everything on a massive rewrite, organizations can:
- Deliver improvements continuously
- Reduce technical debt gradually
- Scale with confidence
- Preserve business continuity
Legacy systems are not obstacles—they are foundations. With the right architectural strategy, they can evolve into modern, resilient platforms.
Modernization should not feel like demolition.
It should feel like growth.