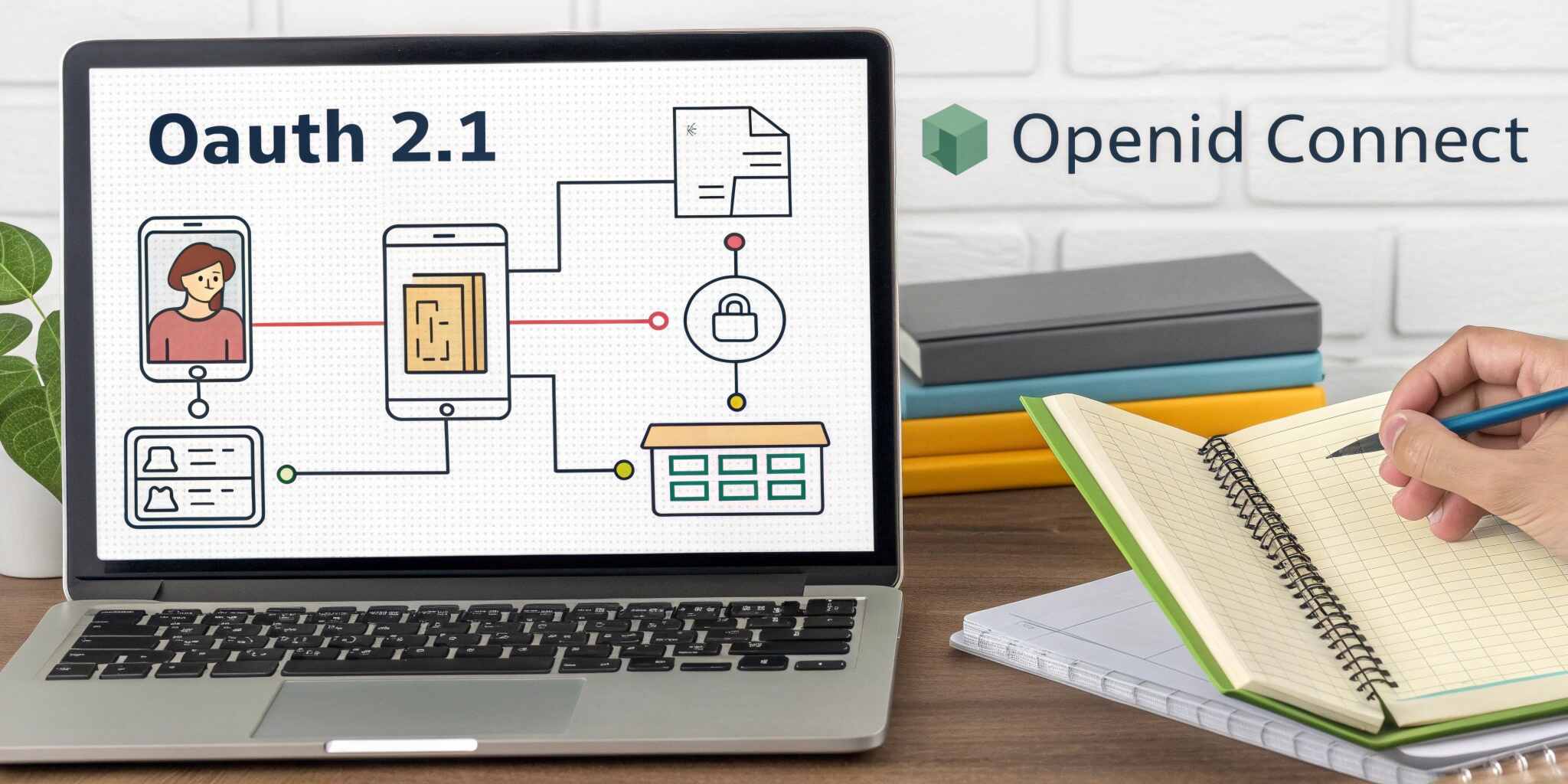
Modern web applications rarely exist in isolation. Users expect seamless login experiences, single sign-on across platforms, and secure access to APIs from browsers, mobile apps, and third-party services. Meeting these expectations requires robust identity standards. OAuth 2.1 and OpenID Connect (OIDC) have emerged as the backbone of modern authentication and authorization on the web.
The Evolution from OAuth 2.0 to OAuth 2.1
OAuth 2.0 introduced a flexible framework for delegated authorization, but its flexibility led to inconsistent and sometimes insecure implementations. OAuth 2.1 consolidates best practices and removes legacy flows that are no longer considered safe.
Key improvements in OAuth 2.1 include:
- Mandatory use of PKCE
- Removal of the implicit grant
- Stronger guidance on redirect URI validation
- Emphasis on secure token storage
OAuth 2.1 is not a completely new protocol—it is a hardened, opinionated evolution of OAuth 2.0.
OAuth Is Authorization, Not Authentication
One of the most common misunderstandings is using OAuth for authentication. OAuth defines who is allowed to access what, not who the user is. It issues access tokens that grant permission to protected resources.
Using OAuth alone for authentication leads to security vulnerabilities and unreliable identity verification. This gap is filled by OpenID Connect.
OpenID Connect: The Identity Layer
OpenID Connect builds on OAuth by adding a standardized identity layer. It introduces ID tokens, which securely convey information about the authenticated user.
OIDC defines:
- Standard identity scopes
- A user info endpoint
- A consistent authentication flow
- Cryptographically signed ID tokens
This allows applications to authenticate users in a reliable and interoperable way.
Understanding Token Types
OAuth and OIDC rely on multiple token types, each serving a specific purpose:
- Access tokens authorize API requests
- Refresh tokens obtain new access tokens
- ID tokens represent authenticated user identity
Proper token lifecycle management is critical to system security.
Authorization Code Flow with PKCE
The authorization code flow with PKCE is the recommended flow for modern applications. It protects against authorization code interception and token leakage, making it suitable for both confidential and public clients.
This flow ensures that tokens are exchanged securely and never exposed to the browser or malicious intermediaries.
Securing APIs with OAuth 2.1
OAuth 2.1 enables fine-grained access control through scopes and resource-specific permissions. APIs validate access tokens before serving requests, ensuring that only authorized clients can perform actions.
Token introspection, JWT validation, and audience checks help prevent token misuse across services.
Single Sign-On and Federated Identity
OpenID Connect enables seamless single sign-on across applications and platforms. Users authenticate once with an identity provider and gain access to multiple services without repeated logins.
Federated identity also allows integration with external providers while maintaining centralized security policies.
Common Security Pitfalls
Despite strong standards, many implementations fail due to misconfiguration. Common issues include:
- Storing tokens insecurely
- Overly broad scopes
- Missing token expiration checks
- Weak redirect URI validation
Security is only as strong as the weakest implementation detail.
OAuth and OIDC in Microservices Architectures
In microservices environments, OAuth and OIDC act as a centralized trust mechanism. Services validate tokens rather than authenticating users directly, reducing duplication and improving consistency.
This approach scales well across distributed systems while maintaining strong security boundaries.
Compliance and Future-Proofing
OAuth 2.1 and OpenID Connect align well with regulatory requirements such as GDPR and data protection standards. Their standardized, auditable flows make them suitable for enterprise and regulated environments.
As identity threats evolve, these standards continue to adapt, making them a future-proof choice for modern web platforms.
Final Thoughts
OAuth 2.1 and OpenID Connect are not just protocols—they are foundational building blocks for secure digital identity. By understanding their roles, strengths, and limitations, engineering teams can design authentication and authorization systems that are secure, scalable, and ready for the future of the web.